Security on Immutable X
This module covers the security protocols of Immutable X, focusing on the use of StarkEx technology, consensus security, and mechanisms to protect user assets and transactions.
StarkEx Technology and Security
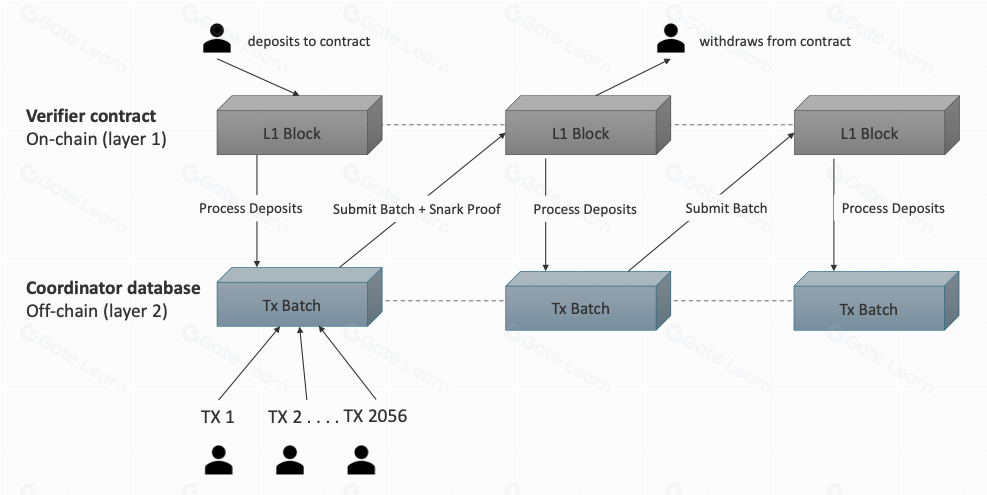
As it was covered in previous modules, Immutable X uses StarkWare’s StarkEx technology, which relies on zero-knowledge proofs (STARKs - Scalable Transparent Arguments of Knowledge). This approach ensures that transactions processed off-chain are verified on-chain with strong security guarantees.
STARK proofs validate the legitimacy of batched transactions, ensuring that only valid state changes are recorded on the Ethereum mainnet. This process enhances scalability and security by batching multiple transactions and validating them in a single instance on-chain, reducing gas fees and increasing throughput.
StarkEx enables Immutable X to handle up to 9,000 transactions per second (TPS) for trades and 18,000 TPS for transfers, with a throughput that is significantly higher than Ethereum’s mainnet, which handles approximately 15 TPS. This technology ensures that transactions remain secure while offering the scalability necessary for high-demand applications like gaming and NFTs.
Consensus Security
Immutable X operates as a zk-rollup, which batches transactions and generates STARK proofs for validation on the Ethereum mainnet. The proofs ensure that only valid transactions are processed, preventing fraudulent activities even if the Immutable system is compromised. This rollup approach leverages Ethereum’s robust consensus mechanism for security.
Unlike sidechains or bridges, which may rely on less secure consensus mechanisms, zk-rollups maintain a verified state on the Ethereum mainnet. This ensures that any updates to the state must be validated through a secure proof, protecting assets and transactions from fraudulent modifications. This trustless model enhances security by not relying on a separate consensus mechanism vulnerable to attacks.
Security Audits
Immutable X’s security framework includes audits by third-party security firms. StarkEx has undergone thorough audits by reputable auditors such as PeckShield. These audits examine smart contracts, protocols, and system architecture to identify and mitigate potential vulnerabilities. Continuous auditing ensures that any security gaps are promptly addressed, maintaining a high level of protection for users.
User Asset Protection
Immutable X employs several mechanisms to protect user assets. The use of non-custodial wallets ensures that users retain full control over their private keys and assets. Immutable does not have access to users’ private keys, minimizing the risk of centralized points of failure. Advanced security measures, such as two-factor authentication (2FA) and heuristic-based detection systems, are implemented to prevent unauthorized access and fraudulent activities.
In the event of a security breach or system failure, Immutable X has robust fallback mechanisms. If the Immutable service becomes unavailable, users can withdraw their assets directly from the Ethereum mainnet using the “full withdrawal” process. This involves interacting with the L1 bridge contract, ensuring that users can always access their assets regardless of Immutable’s operational status.
Bridge Security
When it comes to the security of bridging assets between Layer 1 (Ethereum) and Layer 2 (Immutable X), unlike sidechains, which may use multisig setups vulnerable to attacks, zk-rollups use a verified state model. This helps to ensure that bridge transactions are validated and secure, preventing fake state transitions. Users can trustlessly bridge their assets back to Ethereum, knowing that the process is secured by Ethereum’s consensus.
Immutable X uses a rollup approach to bridge security, maintaining a verified state on Ethereum’s mainnet. This ensures that any state changes must be validated through secure proof, protecting assets from fraudulent modifications. If Immutable fails to process a withdrawal, users can still use a “full withdrawal” mechanism, ensuring that they can access their assets directly from the Ethereum mainnet.
Data Availability
Data availability is the guarantee that all data necessary to verify and reconstruct the state of a blockchain or a rollup is accessible. This matters a great deal when it comes to maintaining security and integrity of decentralized systems, particularly in Layer 2 (L2) solutions, like Immutable X.
Immutable X addresses this problem by ensuring that all necessary data to reconstruct the state is available on-chain. This approach prevents issues related to data unavailability, which can occur if the operator becomes malicious or goes offline. By requiring data to be posted on Ethereum L1 before state updates, Immutable X ensures that users always have access to the information needed to verify their assets and transactions.
Highlights
- StarkEx Technology: Uses zero-knowledge proofs to validate off-chain transactions on-chain.
- Consensus Security: Relies on Ethereum’s robust consensus for verified state transitions.
- Security Audits: Undergoes regular audits by third-party security firms.
- User Asset Protection: Implements non-custodial wallets and advanced security measures.
- Bridge Security: Ensures secure bridging between Layer 1 and Layer 2 with verified state models.