Beware of Unexpected NFTs and Assets in Your Wallet — They Could Steal All Your Funds
This article explores why NFT holders have become prime targets for hackers, analyzing common NFT theft tactics such as sudden increases in wallet assets. Through real-world cases, we’ll uncover the hidden threats of NFT scams and provide practical security tips to help you protect your assets and boost wallet security.Overview
With the rapid development of cryptocurrency and blockchain technology, NFTs (non-fungible tokens), as unique digital assets, have attracted a flood of investors and collectors. However, alongside the booming market lies a growing set of risks.
Have you ever noticed unexpected NFTs or other assets suddenly appearing in your wallet? These seemingly harmless digital items may carry serious security threats — even leading to a complete loss of funds. This article will uncover the hidden dangers behind these scenarios and offer practical security advice to help you safeguard your digital assets more effectively.
Currently, the total market value of cryptocurrencies and NFTs has surpassed $3 trillion, with over 300 million participants worldwide. However, as the market flourishes, it has also become a prime target for hackers and scammers. According to data from Comparitech (as of March 13, 2025), crypto and NFT-related scams have already caused losses amounting to $27 billion — and the number is still rising.

Source: https://www.comparitech.com/crypto/cryptocurrency-scams/ (March 13, 2025)
Why NFT Holders Are Prime Targets for Hackers
1. The Allure of High-Value Assets
NFTs often carry significant value — especially those from rare or hyped collections like Bored Ape Yacht Club or CryptoPunks, where a single piece can be worth hundreds of thousands or even millions of dollars.
These high-value digital assets act like “gold mines” in the virtual world, naturally drawing the attention of hackers. Compared to traditional financial assets, NFT transactions are faster and harder to trace. Once stolen, hackers can quickly cash out the assets.

Source: https://opensea.io/collection/boredapeyachtclub
2. Blockchain’s Anonymity and Irreversibility
Blockchain’s anonymous nature provides privacy for users but also creates a haven for hackers. Once an NFT or token is stolen, the thief can swiftly transfer it to other wallets or launder it using mixers like Tornado Cash.
Because blockchain transactions are irreversible, victims have little to no chance of recovery unless the hacker voluntarily returns the asset or is caught by law enforcement. This makes attacking NFT holders a low-risk, high-reward strategy for cybercriminals.
3. Generally Low Security Awareness Among Users
Many NFT users are newcomers to blockchain and crypto tech, lacking proper security awareness. They may not fully understand the importance of private keys or seed phrases, or know how to recognize phishing sites and malicious contracts.
For instance, some users click suspicious links without hesitation or store their private keys in unsafe places like phone notes or cloud services — all of which open the door for hackers.
4. A Complex Ecosystem Increases Exposure
The NFT ecosystem spans wallets, trading platforms (like OpenSea), smart contracts, and social media (such as Discord and Twitter). Each component is a potential attack vector.
5. Highly Active Communities and Fast Information Spread
NFT users are usually active on platforms like Twitter and Discord, frequently sharing their collections, trade records, or participating in events. This kind of public visibility makes them easy targets. For example, someone showing off a million-dollar NFT on Twitter could immediately attract hackers who then send phishing links or pose as fake support agents.
6. High Technical Barriers That Invite Mistakes
Engaging with NFTs requires a certain level of technical know-how — like using MetaMask, understanding gas fees, and signing smart contracts. For users unfamiliar with these processes, it’s easy to make critical errors. Some might unknowingly grant permissions to malicious contracts or operate in unsecured network environments, leading to theft.
7. Low Cost, High Reward for Hackers
Compared to traditional cyberattacks like breaching bank systems, targeting NFT users is relatively low-cost. A hacker might only need to set up a fake website, send a phishing email, or scatter malicious links across social media — and they could gain access to valuable wallets. Once successful, the rewards can be thousands to millions of dollars. This high-reward, low-risk setup makes NFT users a top target.
Common NFT Theft Methods
Malicious Smart Contracts
NFTs are typically tied to smart contracts, which govern ownership, transfers, and various interactions. Users often receive NFTs from unknown sources, such as social media, airdrops, or websites.
While the NFT itself may appear harmless, its underlying smart contract might contain malicious code. Hackers can exploit this code to gain wallet permissions without your knowledge, ultimately draining all assets from your wallet.

Source: https://trezor.io/support/a/malicious-smart-contracts
Phishing Attacks and Social Engineering
Hackers often create fake websites, emails, or social media messages to trick users into entering their private keys or seed phrases, or into approving unknown smart contracts. For example, you might receive a fake “OpenSea Notification” asking you to “verify your wallet.” But once you click the link and grant access, your NFTs and tokens can be instantly stolen.
In addition, hackers use phishing and social engineering tactics to send malicious NFTs directly to users’ wallets. Simply viewing or interacting with one of these NFTs could allow hackers to exploit smart contract vulnerabilities, potentially gaining control over the wallet or tricking the user into signing high-risk transactions. Always verify the source of any NFT — never interact with unknown or suspicious assets.
On platforms like Discord and Telegram, hackers may impersonate support staff, developers, or community members, claiming they can help “fix” wallet issues. They then persuade users to disclose their seed phrases, ultimately stealing their assets.
Most major NFT projects now include “Scam Report” channels in their servers. Since July 2021, over 75,000 messages have been logged in these channels across various NFT platforms — with 76% of them sent in 2022 alone.

Source: https://beinsure.com/nft-thefts-and-financial-crime-7-types-of-scams-in-non-fungible-tokens/
Hackers also use “blind signing” techniques via eth_sign to steal assets. Unlike traditional phishing transactions that display clear transaction data and incur gas fees, blind signing only shows an obscure string of text — making it highly deceptive. Once the user signs, the hacker can immediately transfer tokens from the wallet.
Fake NFT Projects
Some hackers impersonate popular NFT projects to lure users into buying or interacting with fake platforms. As soon as you connect your wallet to one of these malicious websites, it could trigger smart contracts designed to steal your assets.
Scammers often exploit the SetApprovalForAll() function in ERC-721 and ERC-1155 standards, tricking victims into unknowingly granting full control of their NFTs. Once approved, hackers can transfer assets at any time without further user input. Therefore, before interacting with any NFT project, always verify its authenticity and regularly use tools like Revoke.cash to review and remove unnecessary approvals.
Malicious Code, Software, and Hidden Theft
Installing unknown software or browser extensions (such as fake MetaMask plugins) can infect your device with malware capable of stealing private keys or tracking your activity.
Beyond malicious smart contracts, some NFTs and digital assets may contain scripts that execute upon viewing or interaction. For example, simply clicking on these NFTs might run code that transfers assets to a hacker-controlled address. While these scripts don’t usually compromise device security directly, they can silently drain your wallet.
NFT Bundle Scams with Counterfeits
Hackers often create fake NFT bundles that include either high-quality counterfeits or NFTs embedded with malicious contracts. These bundles tempt users with low prices and the promise of saving on gas fees. However, initiating a transaction may silently authorize SetApprovalForAll(), giving hackers full control over the user’s wallet.
For instance, when purchasing an NFT bundle on OpenSea, always verify the source of each NFT and associated contract. That gas fee “savings” could turn into a costly mistake.

Source: https://opensea.io/collection/boredapeyachtclub
Pump-and-Dump Scams
Scammers artificially inflate NFT prices by hyping up projects via social media or celebrity endorsements, creating a false sense of demand. Once prices peak, insiders dump their holdings, causing a market crash and leaving buyers with devalued assets.
To avoid such schemes, always check an NFT’s transaction history. Legitimate NFTs usually have a diversified base of buyers and organic activity.
Rug Pulls
In these scams, developers lure users into purchasing NFTs with grand promises, only to vanish after collecting funds. These often involve anonymous teams with flashy roadmaps and no real intent to deliver.
For example, in 2021, the creators of Evil Ape disappeared after raising nearly $3 million. Similarly, in 2022, the Frosties NFT project defrauded investors out of $1.3 million. Though the perpetrators were eventually arrested and charged, the stolen NFTs and funds were never recovered.
To avoid rug pulls, prioritize projects with transparent, accountable teams and realistic roadmaps. Verify that development is progressing as promised.

Source: https://www.cbr.com/evolved-apes-nft-disappears-3-million/
Fake NFT Offers
Scammers may impersonate legitimate platforms and send phishing emails to NFT holders, promoting fake offers or discounts. These emails lead to phishing sites designed to steal login credentials or seed phrases.
To protect yourself, always verify the sender’s email address and manually navigate to official platforms in your browser. Never click suspicious links from emails, even if they appear legitimate.
Real-World NFT Scam Cases
1. Interacting with a Suspicious NFT — AJ Loses $41,300 (2021)
On September 21, 2021, X user AJ (@babbler_dabbler) tweeted that his wallet had been compromised, including the theft of The Currency, an NFT by renowned artist Damien Hirst. According to AJ, his only mistake was interacting with an unfamiliar NFT that suddenly appeared in his wallet. That action triggered a wallet breach, resulting in the loss of 13.75 ETH — roughly $41,300.

Source: https://x.com/babbler_dabbler/status/1439987074594217986
2. Jay Chou’s Bored Ape NFT Stolen (2022)
In April 2022, Taiwanese pop star Jay Chou revealed on social media that his Bored Ape Yacht Club NFT had been stolen. The NFT was estimated to be worth around $500,000. Chou stated that the theft occurred after he unknowingly clicked a phishing link.
Hackers likely used social engineering, possibly impersonating fans or project staff, to send a malicious link. After clicking it, Chou unknowingly approved a malicious smart contract, allowing hackers to transfer the NFT. The asset was quickly resold multiple times, making it extremely difficult to trace.

Source: https://cnalifestyle.channelnewsasia.com/entertainment/jay-chou-bored-ape-nft-stolen-308766
3. OpenSea Phishing Attack (2022)
In early 2022, users of NFT marketplace OpenSea fell victim to a massive phishing campaign. Hackers sent fake emails and set up spoofed websites, luring users into signing malicious smart contracts. Within hours, attackers stole 254 NFTs worth approximately $2.5 million, including high-value items from Bored Ape Yacht Club and Decentraland.
Hackers impersonated OpenSea in emails, warning users about “account security issues” and prompting them to “verify” or “migrate” their NFTs. Many users failed to verify the link’s legitimacy and were redirected to a phishing site, where they unknowingly approved malicious contracts that led to asset theft.

Source: https://www.halborn.com/blog/post/explained-the-opensea-phishing-hack-february-2022
4. Moonbirds NFT Scam — $1.5 Million Stolen (May 2022)
Hackers circulated a malicious link that tricked users into signing transactions. This resulted in the theft of 29 Moonbirds NFTs, valued at an estimated 750 ETH — about $1.5 million at the time.

Source: https://x.com/CirrusNFT/status/1529296043547865088
5. AI Voice Deepfake Scam (2023)
In mid-2023, hackers used AI to mimic the voices of corporate executives and trick finance team members into wiring large sums of money. According to a 2023 report from TRM Labs and blockchain analytics firm Chainalysis, the funds — totaling several million dollars — were laundered through crypto mixers.
6. Orbit Bridge Cross-Chain Protocol Hack — $80 Million Stolen (Dec 31, 2023)
On New Year’s Eve 2023, hackers exploited vulnerabilities in cross-chain bridge Orbit Bridge, stealing over $80 million in crypto assets (including ETH and USDC). The breach is suspected to be due to insider key leakage. Part of the stolen funds were laundered through decentralized protocols.

Source: https://x.com/bitinning/status/1741783830372155620
7. DMM Bitcoin Private Key Leak — $300 Million Heist (May 31, 2024)
Japan’s long-standing exchange DMM Bitcoin suffered a historic breach when hackers used leaked private keys to transfer $300 million worth of Bitcoin to over 10 separate addresses. The exchange attempted on-chain tracking and asset freezing, but the attackers used mixers to launder funds, highlighting severe weaknesses in private key security and custodial practices.

Source: https://www.elliptic.co/blog/dmm-bitcoin-loses-308-million-in-unauthorized-leak
How to Protect Your Digital Assets
In the blockchain world, security threats are everywhere. Building a layered defense system — consisting of physical isolation, operational safeguards, and emergency response — can significantly reduce the risk of asset theft.
Layer 1: Physical Isolation (Hardware Wallets & Asset Diversification)
- Use hardware wallets (e.g., Ledger, Trezor) to store high-value assets.
- Hardware wallets are isolated from the internet and authorize transactions only when physically connected and confirmed, greatly reducing the risk of remote hacks.
- Avoid storing large amounts of crypto in hot wallets (e.g., MetaMask) for extended periods.
- Distribute your assets across multiple wallets to prevent single points of failure.
- Separate wallets based on use cases (e.g., trading wallet, long-term storage wallet, daily-use wallet).
- Store critical assets in cold wallets (offline storage) to avoid exposure to online attacks.

Source: https://www.ledger.com/
Layer 2: Operational Safeguards (Careful Approvals & Smart Contract Checks)
Be cautious with links and avoid scams
Watch out for phishing attacks:
Official teams will never ask for your private key or seed phrase via Telegram, Discord, or X (Twitter) DMs. Any request for this information is a scam.Verify project authenticity:
Before interacting, double-check the project’s social media, official announcements, and sources to ensure legitimacy.Manage Smart Contract Approvals Carefully
Double-check website URLs and contract addresses before connecting your wallet or signing any transaction. Fake websites and malicious contracts are a major threat.
Use tools like Revoke.cash or Etherscan’s Token Approval Checker to routinely revoke unnecessary smart contract permissions, limiting the potential for hackers to exploit pre-approved contracts.Smart Contract Security Audits
Before participating in NFT mints or DeFi projects, use auditing tools (e.g., CertiK, PeckShield, SlowMist) to assess smart contract security. This helps avoid exposure to malicious code or exploitable vulnerabilities.
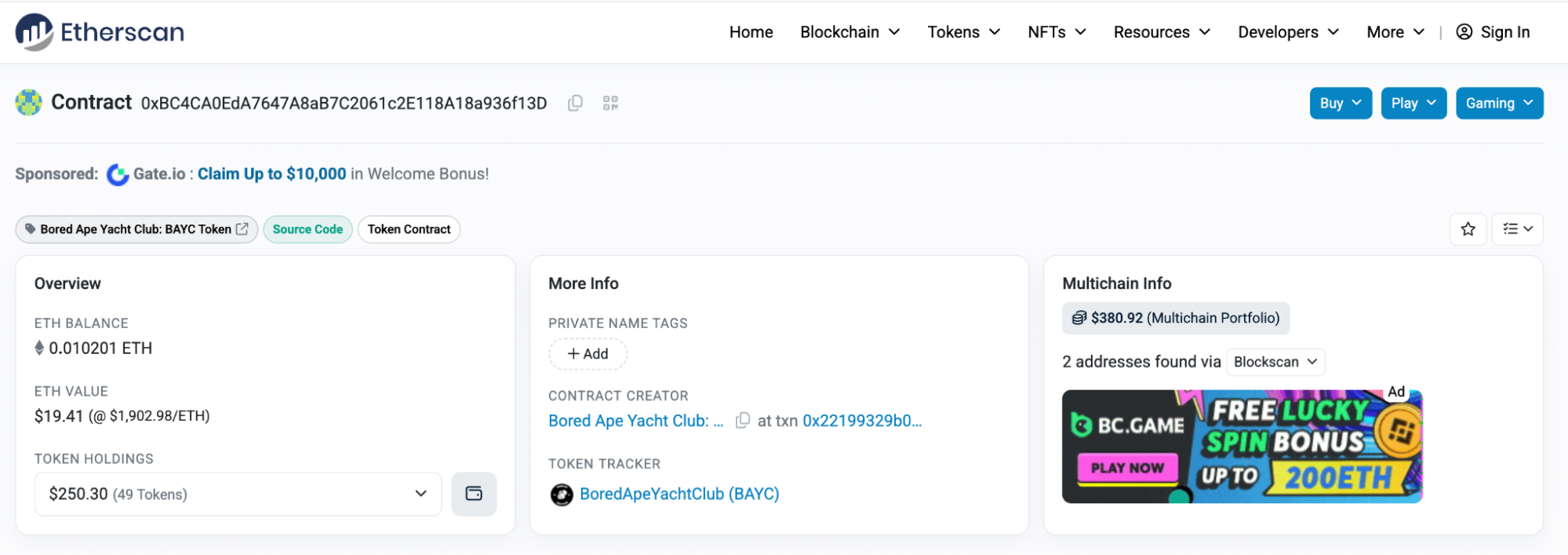
Source: https://etherscan.io/address/0xbc4ca0eda7647a8ab7c2061c2e118a18a936f13d
Layer 3: Emergency Response (If Your Wallet Is Compromised)
If you notice suspicious activity or assets have been stolen, take immediate action:
- Create a new wallet: Generate a fresh private key and store the new wallet’s seed phrase securely using a hardware wallet.
- Revoke malicious contract approvals: Use Revoke.cash or Etherscan’s Token Approval page to cancel authorizations for any suspicious contracts to prevent further losses.
- Transfer remaining assets: Quickly move any remaining funds from compromised wallets to your newly created secure wallet.
- Check your device for malware: Run a thorough virus and malware scan on your computer and phone to ensure your devices haven’t been infected.
- Enable two-factor authentication (2FA): Activate 2FA for all crypto-related accounts — including exchanges and wallet services — to add an extra layer of security.

Source: https://revoke.cash/
Stay Rational — Avoid the FOMO Trap
Don’t Follow the Hype Blindly: Before participating in any project, evaluate its long-term value instead of being driven purely by market sentiment.
Carefully Review Signing Information: When signing a transaction, always verify the contents of the signature to ensure it doesn’t expose your private key or grant malicious permissions.
In the crypto world, security is the top priority. Mastering this three-layered defense system will significantly enhance your asset protection and minimize unnecessary risks.
Conclusion
NFTs and digital assets present unprecedented opportunities, but they also come with serious security concerns. In this digital realm, safeguarding your wallet is just as crucial as protecting a bank account in the physical world. While hackers constantly evolve their tactics, staying vigilant and understanding fundamental security practices can effectively reduce risks.
Hackers target NFT users primarily due to the allure of high-value assets, the irreversibility of blockchain transactions, and generally weak user security awareness. To counter these risks, it’s essential to build a solid security foundation—use cold wallets, regularly audit permissions, and keep your private keys securely stored. Security remains the most critical line of defense in the NFT ecosystem. Only by staying alert can you truly protect your digital wealth.
Related Articles
Top 10 NFT Data Platforms Overview
7 Analysis Tools for Understanding NFTs

How to Do Your Own Research (DYOR)?

What Is Fundamental Analysis?

What Is Ethereum 2.0? Understanding The Merge



